Cybersecurity Awareness: Building a Robust Defense
Introduction
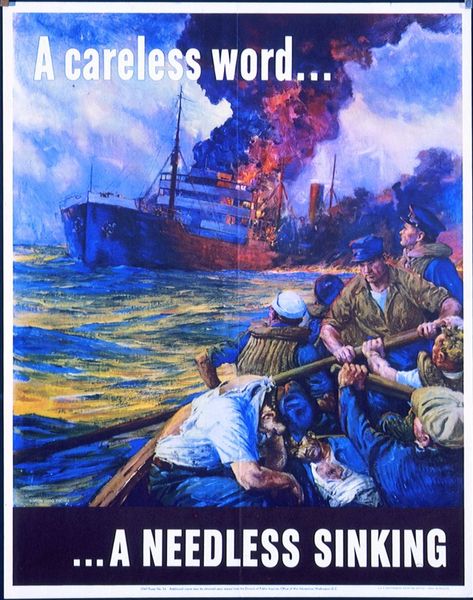
Effective cybersecurity begins with awareness. Since the dawn of critical thinking, humans have sought to protect their physical and informational assets, from ancient conflicts like the Punic Wars to modern global challenges. Today, the digital landscape introduces complex cyber threats that demand vigilance and comprehensive strategies. This article explores the core components of cybersecurity awareness, emphasizing proactive measures to safeguard sensitive information and infrastructure.
Identifying Assets for Protection
The foundation of any cybersecurity strategy is understanding what needs protection. Different assets—such as classified government data or confidential corporate communications—require tailored security measures due to their varying levels of sensitivity. For instance, a breach of government secrets may have national security implications, while leaked company emails could damage reputation or finances. By clearly defining the nature and value of these assets, organizations can develop targeted security policies. Failure to do so risks implementing inadequate defenses or overly restrictive measures that hinder employee productivity.
Fostering Employee Responsibility
Employees are the first line of defense in any organization. Ensuring they understand their responsibilities when handling sensitive information is critical. Non-disclosure agreements (NDAs) are a common tool to outline these obligations clearly, minimizing ambiguity that could lead to misinterpretation. Clear, precise language in NDAs and other policies ensures employees fully grasp the importance of their role in safeguarding data, reducing the likelihood of unintentional breaches.
Establishing Device and Password Policies
In today’s technology-driven world, where computers and mobile devices are ubiquitous, organizations must enforce robust usage policies. A strong password policy—requiring complex, diverse, and sufficiently long passwords—is a fundamental step in protecting digital infrastructure. For example, a weak password like “password” could be a single point of failure leading to a breach. Regular training ensures employees remain informed about best practices, reinforcing the importance of compliance with these policies.
Mitigating Cyber Threats: Malware and Phishing
Cyber threats such as malware and phishing are pervasive and constantly evolving. Awareness and recognition of these risks are essential to neutralize their impact. Employees trained to identify phishing emails or suspicious links can prevent successful attacks. Moreover, prompt reporting of such incidents enables organizations to warn others and mitigate risks across teams. Continuous training on the latest threat vectors.
Addressing Physical Security Risks
While cyber threats dominate modern security concerns, physical security remains vital. Measures such as keycard access, security personnel, cameras, and employee vigilance help mitigate risks like insider threats or social engineering, where unauthorized individuals impersonate employees to gain access. Robust physical security protocols, combined with a culture of alertness, significantly reduce the likelihood of such breaches.
Understanding the Consequences of Security Failures
The repercussions of inadequate security are far-reaching, affecting both individuals and organizations. Employees may face disciplinary actions, including termination, while organizations could suffer financial losses, reputational damage, or even legal consequences, depending on the breach’s severity. Clearly defined consequences in security policies ensure employees understand the stakes, fostering a culture of accountability.
The Ongoing Nature of Security Awareness
Cybersecurity is not a one-time effort but a continuous process. As long as threats—cyber or physical—persist, organizations must remain proactive. Regular training, updated policies, and a commitment to vigilance ensure defenses evolve alongside emerging risks. Assuming security is “complete” is a dangerous oversight; staying ahead requires constant adaptation.
Conclusion
Cybersecurity awareness is the cornerstone of a resilient defense strategy. By identifying critical assets, fostering employee responsibility, enforcing device and password policies, mitigating cyber and physical threats, and preparing for consequences, organizations can build a robust security posture. In an ever-evolving threat landscape, sustained awareness and adaptability are essential for safeguarding sensitive information and ensuring operational integrity.
