The Siren Song of the Internet of Things: Convenience at the Cost of Vulnerability
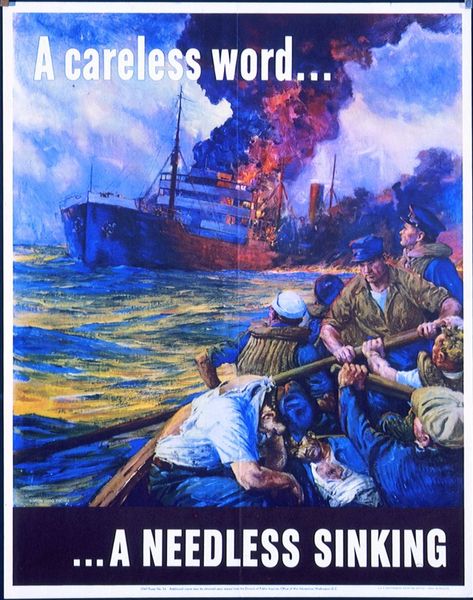
In Ancient Greek mythology, sailors navigating the Mediterranean and Aegean seas faced myriad perils, none more beguiling than the sirens. These creatures, often depicted as half-woman, half-bird, used their enchanting songs to lure mariners to their doom, their ships shattered against treacherous rocks. Though rooted in ancient lore, the siren’s allure serves as a potent metaphor for a modern phenomenon: the rise of the Internet of Things (IoT) and its promise of convenience at the potential cost of security and privacy.
The Allure of the Smart Home
In today’s fast-paced world, convenience is king. The advent of “smart homes” exemplifies this, offering unparalleled control over one’s living environment through a single device: the smartphone. Forgot to lock the door while miles away? A few taps on your phone resolve the issue. Left the lights on? Your phone has you covered. Cozy in bed but need the lights off? Reach for your phone. The ability to manage nearly every aspect of a home remotely appeals to those who prioritize efficiency and peace of mind. For anxious homeowners, the knowledge that potential oversights can be rectified instantly is a powerful draw.
Tech enthusiasts, too, are captivated by IoT devices. These early adopters eagerly embrace cutting-edge technology, often camping outside stores to secure the latest iPhone or iPad. Their enthusiasm fuels the rapid adoption of smart home systems, transforming houses into interconnected hubs of innovation.
The Hidden Dangers of Connectivity
Yet, much like the sirens’ songs, the promise of IoT may conceal significant risks. The very devices designed to enhance security and convenience can erode privacy and expose users to new vulnerabilities. IoT devices generate vast amounts of data, which companies often collect and share with advertisers. A smart home equipped with connected thermostats, cameras, and appliances becomes a treasure trove of personal information, enabling advertisers to craft highly targeted campaigns. This unprecedented access to consumer data raises serious privacy concerns, as individuals trade personal information for convenience.
Moreover, the reliance on smartphones as the central control hub for IoT devices introduces a single point of failure. Losing a phone is inconvenient; losing control of your smart home is catastrophic. A malicious actor with access to a homeowner’s phone could manipulate connected devices, from unlocking doors to disabling security systems, all without needing to be physically present. While a stolen key poses a localized threat, a compromised phone grants remote access to an entire home, amplifying the potential for harm.
Beyond the Home: IoT in Automobiles
The IoT’s reach extends beyond the home, infiltrating industries like automotive manufacturing. Tesla, led by visionary entrepreneur Elon Musk, has become synonymous with innovation in electric vehicles. Features like self-driving capabilities and remote summoning—where a car can be called to its owner’s location via a smartphone app—represent remarkable technological achievements. Forgetting where you parked is no longer a concern; your car comes to you. Yet, these advancements come with vulnerabilities. A hacked vehicle could be manipulated remotely, posing risks to both the owner and others on the road. The integration of IoT into cars transforms them from mechanical assets into potential cyber liabilities.
A Modern Siren’s Call
At its core, the proliferation of IoT devices increases individual vulnerability. In the year 2000, cyber threats were largely confined to computers. Today, nearly two decades into the 21st century, the average person is surrounded by a constellation of internet-connected devices, each a potential entry point for cyberattacks. A single compromised device—be it a smart lock, thermostat, or vehicle—could have cascading consequences, undermining the very security it was meant to enhance.
The allure of IoT is undeniable, promising a life of ease and efficiency. Yet, much like the sailors of ancient Greece, we must navigate these tempting waters with caution. For some, the risks outweigh the rewards, leading them to favor traditional, mechanical solutions—like a sturdy lock—that offer reliability without the specter of cyber vulnerabilities. As we chart the future of technology, we must ask ourselves: is the convenience of the IoT worth the price of our privacy and security? Or are we, like the sailors of old, being lured toward unseen rocks by a modern siren’s song?