Cybersecurity Threats to the U.S. Power Grid
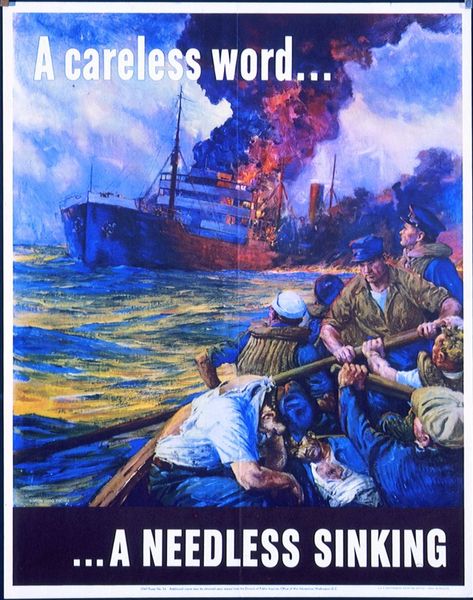
The power grid is a cornerstone of modern society, seamlessly powering homes, businesses, and critical infrastructure. Yet, its reliability is so ingrained in daily life that it often goes unnoticed—until it fails. While cyber-attacks on personal devices or corporate networks dominate headlines, the notion of a cyber-attack targeting the power grid may seem improbable. However, the 2015 cyber-attack on Ukraine’s power grid, which disrupted electricity for several hours, demonstrated that such an event is not only possible but could have far-reaching consequences if prolonged. This incident raises a critical question: could the United States face a similar threat, and if so, how prepared is the nation to respond?
The Complexity of Attacking a Power Grid
A cyber-attack on a power grid is not akin to hacking a single computer. It requires meticulous orchestration, exploiting vulnerabilities in complex, interconnected systems that blend operational technology (OT) with information technology (IT). Power grids rely on supervisory control and data acquisition (SCADA) systems, which manage electricity distribution, and these systems are increasingly digitized, making them potential targets. The Ukraine attack, attributed to sophisticated actors, involved malware that disrupted control systems, highlighting the level of expertise required for such an operation.
While the Ukraine outage lasted only a few hours, a prolonged disruption—lasting days or weeks—could be catastrophic. The U.S. power grid, while robust, is not immune. Though the likelihood of a successful, large-scale cyber-attack remains low due to the grid’s complexity and existing safeguards, even a small risk warrants serious preparation.
Potential Consequences of a U.S. Power Grid Attack
A sustained power outage across multiple states would unleash widespread disruption. The economic toll could reach hundreds of millions, if not billions, of dollars, affecting industries, supply chains, and essential services. Hospitals, reliant on electricity for life-saving equipment, could face dire challenges, potentially leading to loss of life. Water treatment plants, transportation systems, and communication networks would also be compromised, amplifying the chaos. Such an attack, given its scale and intent, would likely be classified as an act of war, triggering significant geopolitical ramifications.
Current Preparedness and Gaps
U.S. power companies have developed contingency plans to address such scenarios, emphasizing rapid response and coordination. These plans involve collaboration among utilities to restore power quickly and communication with federal and state governments, particularly in multi-state incidents. The Department of Energy and the Federal Energy Regulatory Commission (FERC) play key roles in overseeing grid security, while the North American Electric Reliability Corporation (NERC) enforces cybersecurity standards, such as the Critical Infrastructure Protection (CIP) protocols.
Despite these efforts, some cybersecurity experts argue that current plans have significant shortcomings. Vulnerabilities include outdated infrastructure, inconsistent adoption of cybersecurity best practices across utilities, and insufficient simulation of large-scale attack scenarios. For instance, many systems still rely on legacy equipment that predates modern cybersecurity threats, making them harder to secure. Additionally, the decentralized nature of the U.S. grid, while a strength in some respects, can complicate coordinated responses.
Recommendations for Enhanced Resilience
To bolster defenses, power companies and regulators should prioritize the following:
-
Modernize Infrastructure: Upgrade legacy systems with secure, resilient technologies and implement robust encryption for SCADA and other critical systems.
-
Enhance Cybersecurity Standards: Strengthen NERC CIP requirements, ensuring uniform compliance across all utilities, and conduct regular audits to identify weaknesses.
-
Conduct Realistic Simulations: Perform large-scale, multi-utility cyber-attack drills to test response plans and identify gaps in coordination.
-
Foster Public-Private Collaboration: Deepen partnerships between utilities, government agencies, and cybersecurity firms to share threat intelligence and best practices.
-
Invest in Workforce Training: Equip grid operators with advanced cybersecurity skills to detect and mitigate threats in real time.
Conclusion
The U.S. power grid remains a critical yet underappreciated lifeline. While a cyber-attack on the scale required to cause widespread disruption is unlikely, the potential consequences are too severe to ignore. The 2015 Ukraine attack serves as a stark reminder of what is possible, and the U.S. must take proactive steps to fortify its defenses. By addressing vulnerabilities, enhancing response plans, and fostering collaboration, the nation can better safeguard its power grid against an evolving cyber threat landscape, ensuring the lights stay on for all.